Dan Bustillo:: Thanks for letting me interview you, Tim! Excited to get started! As an overview, some of the things that your work deals with that I would love to discuss are issues of information, censorship, anonymity, and the organization of information that lends it meaning. But first, can we talk a bit about your upcoming book?
Tim Schwartz:: Hi! Sounds good. I am writing a book on how to be an anonymous whistleblower with the press specifically. It’s a technical guide and an overview of freedom of the press and a history of whistleblowers. There are a number of options for whistleblowers in terms of operating internally, through a corporation, or through a government agency, but most of those lead to retribution. A very high percentage of whistleblowers get some sort of retribution, so by going to the press anonymously, the cost of blowing the whistle hopefully won’t be so steep.
DB:: You also mentioned in an earlier conversation that you are formulating an argument for anonymity…
TS:: Now that we have a device on us, notably the cellphone—which has more information about us than we could fit in a filing cabinet—the idea that you are really going to lock down that information and protect your identity is inaccurate. Even being on the forefront of technology and security, you have to work really hard to limit your data exposure, so in all likelihood we are all going to be emitting data constantly. To protect your identity, it’s much easier to start a new anonymous identity than to protect your real one. You can have your normal identity and let it emit data and then have other identities or pseudo anonymous or anonymous ones that can do other things in the world. Conceptually I think it is really important that we now have the tools to have multiple identities that we can control. I think it is more protective to a core identity and I don’t think that has been argued yet. It is mostly argued that you should either lock down and seal up the data emitting identity, or go for obfuscation, which means to pollute your data streams, but I think the real method that one could adopt is to have these other anonymous identities. For example, this year a lot of people have started using Signal on their phone to send encrypted text messages and phone calls, but Signal is still tied to your phone number, it is not anonymous. Someone could potentially look at the network traffic and see that you and I are communicating, even though the actual message is encrypted. But what if you didn’t have to have that phone number to have a Signal account or an email address? There could be other modes of communicating privately that aren’t tied back to a primary identity.
DB:: Right, because even using Signal still allows for the existence and collection of metadata—the who, where, when of the communication—and as we know, metadata is actually very useful data, whereas what you are proposing kind of bypasses that. Metadata can still be collected but it will differ with each instance of communication.
TS:: That’s the hope!
DB:: Where can folks look for this book when it comes out?
TS:: It will be available online, at OR Books and it should come out in stores at the end of Fall 2018. By the way, my pitch for why to do a printed book and not an online series of guides is that books can still be secure if you buy them in cash and no one can know what you are reading it, whereas if you go buy this book online or on a website without procuring it in a secure way, someone could potentially track that.
DB:: Even if you have downloaded it on a different device?
TS:: Well, no, see that’s where we want people to be. Once folks read the book, hopefully they can use the web anonymously and securely. But right now, most people don’t know how to do that.
DB:: Because if I were to read the online version, I would ostensibly read it in my web browser where I can be traced in a number of ways, if anything by virtue of having an IP address and being connected to the internet, as opposed to downloading it anonymously on a different machine and then printing it out?
TS:: Yes, printing it out or even reading it on a different device would work. I am going to encourage people in the book to print it and pass it around on USB sticks. It will be available for free online with a minimum donation of zero dollars! Oh, and you can also purchase it in bitcoin!
DB:: Do you know about how printers mark material with metadata?
TS:: Yeah, it is called microdots and they have been known about for around for 15 years. I think it was implemented by the FBI with printing manufacturers. Basically, all printers leave micro yellow dots that identity the IP address and the filename of that which is printed, when it is printed, and where it is printed, and it is on everything that gets printed all the time. If you hold a magnifying glass up to the print, you can see the micro dots on every printed piece of paper.
DB:: If printed data can be traced by the time stamp printed onto the paper directly, and if I were to download your book and then print it out, I would still need to download it anonymously, right?
TS:: Yeah, so in the book, for example, I explain how to install Tails, and the thing I recommend is wearing a hat and a hoodie and going to a Kinkos or FedEx and printing out the instructions for Tails there, unless you already have an anonymous device you can put the instructions on, because it is overwhelming to try and do it with 2 USB sticks without instructions and a computer. The book will say on the back something like, Please buy this in cash. Buy copies and pass it to your friends or folks who might find it useful. I also plan on doing a book tour where I will have copies of Tails for folks and I will also bring fake book covers that people can use to hide their books. I know it seems to many folks who don’t use the internet in this way that they are playing spy, but the more you can get in that mindset, the more protections you have.
DB:: As more and more people get into that mindset, how do you think that will affect security culture at large? If I think I am playing spy or I am doing this because I can and not because I need to, does that take away from someone who does need to be anonymous?
TS: The more people that do this, the more it supports people that need it. This is a founding principle of Tor.
DB:: Cool cool, let’s talk about your art! Wait, is the book art?
TS:: Yep!
DB:: This is something I am interested in and I find your practice is rooted in. You have an activist practice and you also have an art practice and they are somewhat interchangeable. Is that fair to say? How do you see the places where they diverge as operating in your respective practices? Like what can art do that activism can’t, and what can activism do that art can’t?
TS:: Personally, I have trouble making art that is the signifier of activism. I make this art sometimes, and I struggle with that, so I try to make art that actually is activism. When the 2010 earthquake hit Haiti, I wrote the precursor to Google Person Finder and I don’t know that that was exactly my art practice but it was just something that I did while in grad school sitting in an art studio. I think that if I wasn’t an artist I would not have thought that it was possible—I have never written a book, why would I write a book? This project started as an art project that was going to be a small guide that I was going to be handed out in D.C. but once I got to that point, I thought it might have a greater impact as a book. Instead of doing a traditional book tour, I will be doing security trainings that are more informal, part performance and part workshop, which I’ve done at museums and other spaces.
DB:: Do you think that art allows you to pull things off that are more experimental but also more daring? Are there legal grey areas you can operate in as an artist that you wouldn’t be able to as a non-artist?
TS:: The other people who might write a book like this are security researchers, lawyers who defend whistleblowers, journalists, or whistleblowers themselves. I think lawyers and journalists might not do it because most journalists can’t be seen as enticing whistleblowers to get information for them, and lawyers can’t give non-legal advice, so that leaves whistleblowers or security trainers who are on the outskirts of the system. I think this is a great space for an artist to work in, because, well, I don’t care about the rules! I care about the legality, but I don’t care what I can and can’t do because it is my art practice and I can choose to do what I want. Thankfully, because we have been doing LA Cryptoparty for a number of years and doing these weird trainings, I have a bio on the back cover that involves security training even though the security training was also an art project. Art is totally weird.
DB:: This brings me to the making of meaning. Data always has meaning and that meaning is derived from the way in which it is arranged or configured, which is why even metadata has meaning. Therefore, it almost makes more sense to use art to address these issues. Here, I am thinking of how the “theater of security” is a term often used in security discourse, which I think is radically mobilized in Ricardo Dominguez’s notion of the “performative matrix,” since through this idea, he basically finds ways to get that theater to perform itself. It seems you are redirecting that performativity by using art to do security trainings and teach-ins. I also think this relates to meaning, there is an artistry and craft to the way meaning is made through arrangements. We can think of this in terms of composition, but this is also how data functions.
TS:: Sometimes making meaning like that can lead to the loss of information. I have had many discussions with archivists and librarians about the loss of information through digital archiving projects, which is also something I address in my work.
DB:: Can it be said that your work does data transformations? There is something about the way data is transformed each time it is transferred and rendered less legible on the one hand but perhaps more legible on the other, or at least legible in a different way, which is interesting to me because it activates the role of the visual and basically tells us what we kind of already know, which is that pure data or raw data can’t be processed by human eyes anyway so everything else is a fiction.
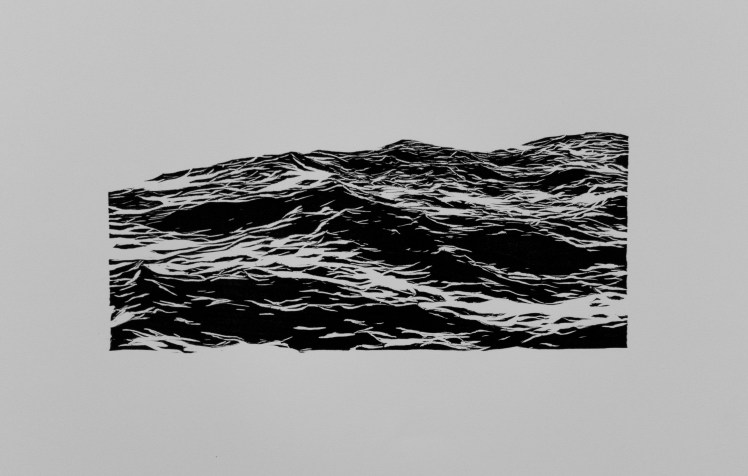
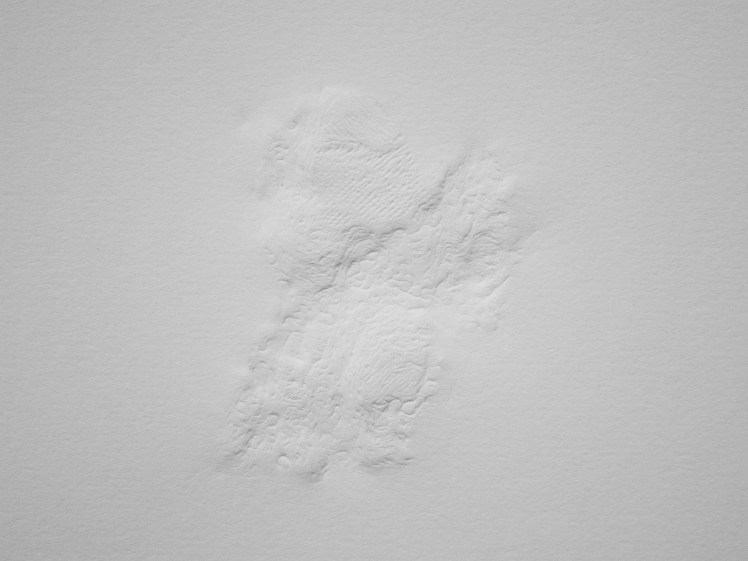
TS:: My argument would be that just looking at it on screens has not removed the data from its native state, so by bringing it back into the physical world, whether with prints, sculptures, or books that you can actually read the data in a different way. I have been making digital topographies for a number of years that are generated with 1s and 0s and algorithms, and with physical processes they translate into something that might look like an ink landscape drawing or a physical topography on paper, but all of them revolve around the translation of digital data into physical. This piece is a diptych called Detritus 1. I took a 3D wave simulation and did a 3D print of it, transferring it to paper by hand burnishing it. I then made a rendering of a 2D view of it and by hand cut a wood block and printed it. As a result, there are 2 ways of looking at the same data but both have been translated into physical space. When you look at either one they feel like a real ocean but they are both algorithmically generated—the original data I used was from the wave modeling algorithm.

DB:: You do something similar in your piece eScapism. Can you describe that piece?
TS:: The e-screens are called electronic paper. I find them super interesting because they are the first screens that don’t require power to hold an image. All other screens need power continuously to do run backlight and change the composition of the pixels, but these screens are actually black and white beads that flip when power is applied. When the power is removed, the image remains locked. I think of them as a digital Rosetta stone, so I hacked them and affixed an image drawn from my digital wave generation tool—essentially these works are pure digital data and in a material form. Also, since the screens are not reflective they look more like paper, so you are actually looking at digital material in a raw form, which you never get to do with traditional screens.
DB:: Because the e-screens don’t require power, I am reminded of another idea you address in your work about a forthcoming digital dark age. Is there one piece in particular that talks about that?
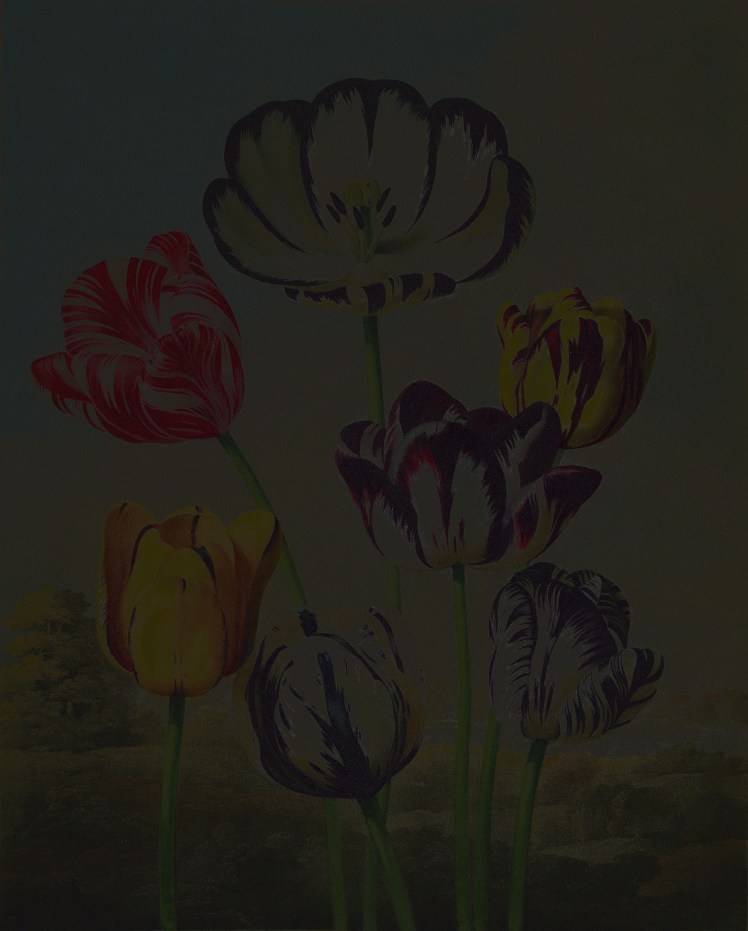
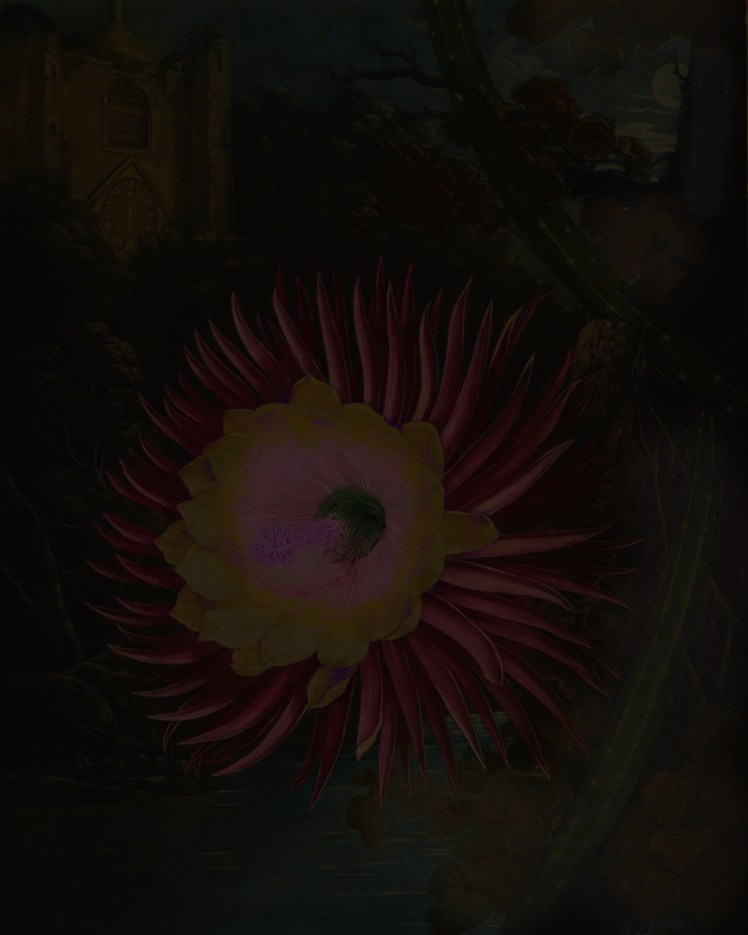
TS:: Yes, this print, Botanical Loss. This piece is about the information that was lost in a high-resolution scan of a botanical image at the Missouri Botanical Garden. There is a book from 1799 called Temple of Flora and it is the first large-format fully illustrated book on botanicals (40 or 50 copies of it still exist, of which the Missouri Botanical Garden has 2 copies). Taschen commissioned high-resolution scans of the book and when I visited the Missouri Botanical Garden, they had taken these high res scans and made high res lossless JPEG2000 copies of them. They put these copies on the Biodiversity Heritage Library website so that scholars can see them around the world. I was able to get the original high resolution scans and I wrote software to compare them pixel by pixel with the JPEG2000 copies to reveal what was lost. Where you see black on the print is where there is no information loss and where you see color, it is the actual color value that was lost in the library’s attempt to construct a lossless digital archive of this image. The idea that you can scan something and make an archival copy is sort of utopic.
DB:: Are you saying there is no true digital copy?
TS:: Yeah. This piece tries to represent the loss that occurs in the copying process to point out the fact that the digital is not a perfect representation of the physical and the idea of digitizing things so they can stay around forever does not work, which lands us in this place of loss without knowing there is loss.
DB:: Until sometime in the future when we no longer have the necessary screens or platforms to support and display these file on. Would that be the digital dark age we are going to experience?
TS:: The digital dark age, in summary, is the idea that because we are creating so much digital information all the time and we don’t have adequate tools to archive them or make them readable forever, there will be things we will be missing. We are only 20 or 30 years into the digital age which might last hundreds of thousands of years, and the chances of us losing the material at the beginning is super high. When we look back at this period of time, the historical record might be blurry because we weren’t able to archive it properly—because frankly, we don’t know what we were doing. This is my favorite apocalypse! Also, there is no incentive for corporations to work on solving this. It is a plausible scenario in the long term, so in our digital worlds where everything is fleeting, and clicks happen, and swipes happen and it is all super-fast, none of that is focused on long-term data retention. My favorite way to explain this, What did it take to get your grandparents’ photos? As long as they were in a shoe box under the bed, and the house didn’t burn down, you got the photos. But what would it take for you to deliver the photos you take today on a cellphone to your grandchild? Inconceivable, right? Physical hard-drives last 3 to 5 years, DVDs around 20 to 30 years, so we don’t have the capabilities to store this stuff forever.
DB:: This is so interesting because in thinking of family photo albums, of course there is always a politics to the archive and family photographs only go so far back. Not every family is photo-documented, and not everyone in the family is photo-documented or has access to taking pictures.
TS:: Yes, and in the digital age, it is probable that archiving might be a pay-to-play situation like those whose family archives withstands time might have had access to something like Apple Vault. So unless you can afford the $500/year, your data won’t be stored; or unless you have time and are able to figure out an alternative highly technical backup plan, you will lose your data. Another changing aspect with archiving is that it used to be a non-active process, in that when die, someone would come in and collect all your papers and your archive was based on that. Whereas now, everyone has to channel their own inner archivist if they want their digital work to live on.
DB:: And that changes the spatio-temporalities we live in. As we live in the present, we are always thinking of a future in which we don’t exist and of how the present in which we do exist will be looked back upon.
TS:: That goes for all the high schoolers who are told to be careful about what they post on Facebook, because those posts will be around forever. If we think about that idea more, it is also probable that laws will change and retroactively render something that once was legal, illegal. That is an argument for why folks should care about data protection and data privacy. Regimes and heads of states can change, as we’ve seen in the past year, and something that is currently legal might become illegal.
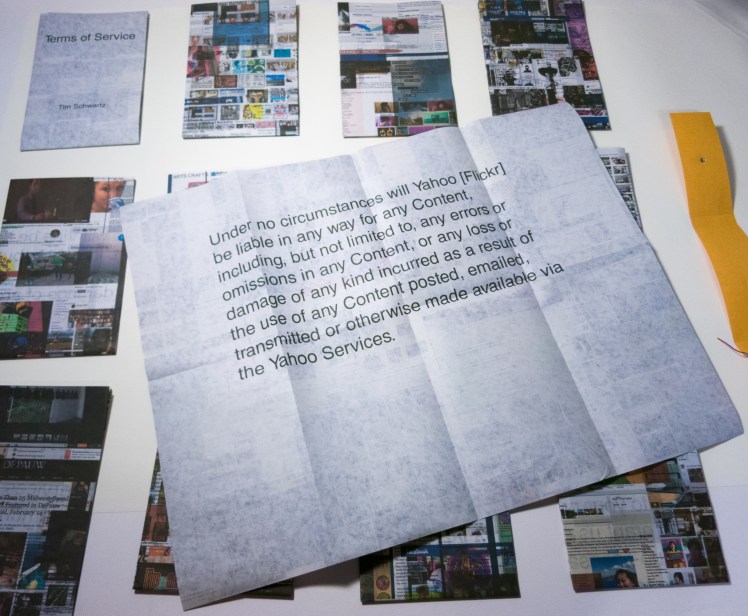
DB:: Can you talk about your piece Terms of Service?
TS:: Terms of Service was a project I did, where I stalked all of the other artists in a group show and made collages out of all their digital material and then juxtaposed it with a term from a terms of service agreements, from one of the services they actively used.
DB:: You stalked them digitally and all the images featured in the printed book were either posted on a social media platform or were collected by a service?
TS:: Yes, exactly. Here is one of the terms of services from Facebook: “We, Facebook, reserve all rights not expressly granted to you.”
DB:: And it doesn’t list what those rights are but either way Facebook has them…
TS:: For U.S. citizens corporations own our data, whereas in Europe for instance, individuals have control over their data even if corporations hold it. In Europe you can write to Facebook and say, please delete my information and give me a copy of it whereas in the U.S. there is no legal requirement for corporations to honor your request. In the U.S., we don’t own our data!
DB:: Yet we have to pretend that we do when we agree to these kinds of terms of services. We act as if we were the sole proprietors of this data when we are not. What isn’t a performance??
TS:: Exactly!
DB:: That is probably a good place to end, with the performance of everything in what will become a digital dark age…